Plugging the Right Holes
NetSPA software maps computer networks to find paths most vulnerable to hacking.
On the night of November 1, 2004, according to published reports, hackers in the Chinese province of Guangdong broke into computers at the Army Information Systems Engineering Command in Arizona, the Defense Information Systems Agency in Virginia, the Naval Ocean Systems Center in California, and the Army Space and Strategic Defense Installation in Alabama. The attack, Time magazine and The Washington Post wrote, was part of Titan Rain, a series of breaches of U.S. government computers that occurred between 2003 and 2005 and may have captured sensitive information about military readiness.
In fact, says electrical engineer Richard Lippmann, a senior staff member in Lincoln Laboratory's Information Systems Technology Group, U.S. government and defense computer networks are attacked all the time. In response to this chronic cyber threat, he and his colleagues developed NetSPA, a software tool to identify potential avenues of attack in computer networks. NetSPA (for Network Security Planning Architecture) uses information about networks and the individual machines and programs running on them to create a graph that shows how hackers could infiltrate them. Although system administrators can examine visualizations of the graph themselves to decide what action to take, NetSPA analyzes the graph and offers recommendations about how to quickly fix the most important weaknesses.
NetSPA relies on vulnerability scanners, such as Nessus, to identify known vulnerabilities in network-accessible programs that might allow an unauthorized person access to a machine. Fast-spreading worms, for instance, often take advantage of weaknesses in servers or operating systems to spread from one machine to another. But simply being aware of vulnerabilities is not sufficient; NetSPA also has to analyze complex firewall and router rules to determine which vulnerabilities can actually be reached and exploited by attackers and how attackers can spread through a network by jumping from one vulnerable host to another.
"It's a matter of what the attacker can get to and in what order," says Kyle Ingols, a computer scientist in Lippmann's group who is working on NetSPA, along with Seth Webster (who is focusing on ways to make the system more automated) and MIT graduate student Leevar Williams (whose master's thesis is on visualizing attack graph data). It takes a long time to patch all hosts in a network. "If you spend time patching vulnerabilities the attacker can’t get to first," Ingols says, "you've left your network exposed longer."
NetSPA aims to solve that problem. "Instead of patching or fixing or blocking a thousand hosts," Lippmann explains, "we could say there are ten critical hosts and patch those first."
The software finds the most critical weaknesses by combining information from vulnerability scanners with firewall rules used to allow and block access and information about the physical structure of the network. For instance, if a firewall allows a certain kind of access, hackers could use that access to reach a vulnerable machine on the inside of the network. That might grant them access to only one machine, but once they take over that machine inside the firewall, they then gain access to many more. Thus, a route through the firewall to a vulnerability on a single "steppingstone" host is much more critical than the potentially many other vulnerabilities on the network.
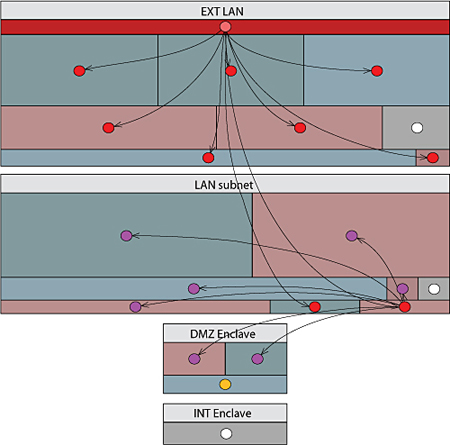
A screen shot shows an attack graph cascade. Each of the four large rectangular regions represents one subnet in a larger network. Within each subnet, the smaller rectangular regions represent groups of hosts that are treated identically by all firewalls and that are compromised by an attacker to the same level. The dot at the center of each region signifies all hosts in that region. The attacker starts at the upper subnet (EXT LAN) on a single host (topmost dark rectangle). Lines connecting hosts represent vulnerabilities that the attacker uses to progressively compromise more hosts. After one hop, the attacker compromises all vulnerable hosts in the upper subnet and jumps to two hosts in the next subnet (LAN subnet). On the next hop, the attacker compromises all vulnerable hosts in the second subnet and jumps to two hosts in the third subnet (DMZ Enclave). On the third hop, the attacker compromises one more host in the third subnet and cannot reach the fourth subnet at the bottom of the display.
This insight sounds obvious, but applying it to real systems can be a huge challenge. A network comprising thousands of computers may have dozens of filtering devices such as firewalls and routers, and each device may have 200 or more different filtering rules. The multitudinous combinations of possibilities are far too many to track down by hand, and are even very complex for a computer algorithm to compute. The original version of NetSPA, in fact, could handle networks of only about 17 machines before the modeling complexities made it too slow to be useful.
Since then, however, the Lincoln Laboratory researchers have developed ways to speed NetSPA up. For instance, firewalls may have rules that treat a number of different machines on the same network in the same way. Rather than modeling each of those machines individually, the software uses the same model for all of them, saving significant computing time. The researchers have also developed new types of attack graphs and efficient algorithms to compute these graphs.
In examining firewall rules, NetSPA also has the potential to discover unforeseen avenues of attack. For example, a network might have had to share data with an outside vendor several years ago, so the system administrator would have added a rule to allow access from that vendor's IP address. That long-forgotten permission could be exploited by someone forging that address.
Lincoln Laboratory researchers have received one patent for the first type of attack graph they developed, called a "predictive" graph, and have one patent pending for a much more efficient and recurrent type called a "multiple prerequisite" attack graph. They're testing NetSPA on different networks and developing ways to make it easier to use. A group of MIT students created a business plan for a proposed company called CyberAnalytix that could commercialize NetSPA (Lippmann and Ingols are technical advisors). This plan won $10,000 in the MIT $100K Entrepreneurship Competition in May. If CyberAnalytix fulfills the students' goals, the tool it sells could provide a protective umbrella in case anything like Titan Rain were to fall again.
|