Keeping an Eye on Cyber Threats
Researchers use real-time data from Lincoln Laboratory networks to monitor and develop countermeasures against cyber threats.
It is a silent threat: as you read through your morning email and catch up on the news, hackers could be working to steal your passwords and sift through your files. Without warning, your private virtual world could become public. Many computer users know how devastating a cyber attack can be. But imagine the same thing happening to your office network. Now imagine it happening to an even larger network, such as that operated by a local government agency or financial institution. In 2014, threat became reality when researchers discovered an Internet security vulnerability named Heartbleed in the widely deployed network security library OpenSSL. Some analysts said Heartbleed had the potential to be the most catastrophic vulnerability ever found.
It allowed hackers to probe web servers by simply sending a short command packet, i.e., a heartbeat packet, to the server. The packet would ask the server to echo information back to the user with extra data attached, leading previously secure websites to "bleed" information that could include private data, such as passwords and credit card numbers. Heartbleed affected more than 500,000 networks, including Lincoln Laboratory's, but the Laboratory's Security Services Department (SSD) and Information Services Department (ISD) had a unique cyber defense resource that allowed them to quickly access the data they needed to identify, assess, and neutralize the threat: the Lincoln Research Network Operations Center (LRNOC).
"When Heartbleed was released publicly, ISD and SSD requested the researchers at LRNOC to help determine its impact and ensure no critical information was leaked," says Tamara Yu of Lincoln Laboratory's Cyber Systems and Operations Group. "Using LRNOC network data, researchers were able to quickly use research tools to assist ISD and SSD in their investigation and assess potential impact. Fortunately, no sensitive information was leaked." Because the risk for a security breach and loss of sensitive information is high, researchers at LRNOC are working on ways to not only fight cyber threats like Heartbleed but also prevent them.
The LRNOC provides an environment in which cyber security researchers and analysts can use live network data to develop and test new techniques for defending Lincoln Laboratory's enterprise network.
For many research purposes, data produced by tools that utilize statistical models can be accurately labeled and can enable repeatable experiments. However, live data are "messy" and include many unusual and unexpected formats. Any algorithm developed to detect attacks needs to be tested out in a "real world" setting in order for developers to truly understand the algorithm's strengths and weaknesses.
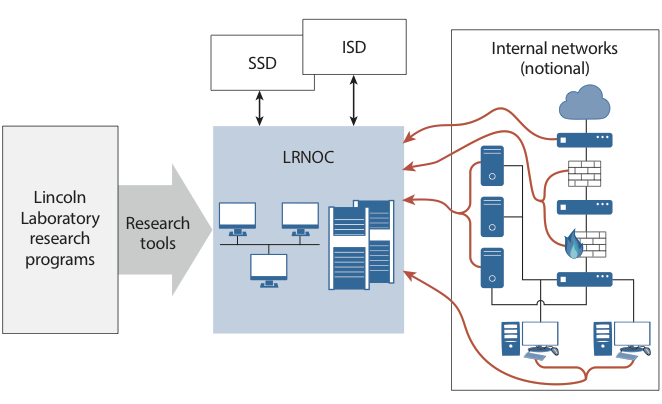
The Lincoln Research Network Operations Center (LRNOC) is the hub of cyber traffic research at Lincoln Laboratory. It gathers information from internal networks (right) and shares important information (potential threats) with the Security Services Department (SSD) and Information Services Department (ISD). Research teams also use LRNOC network traffic and data to create cyber security tools. |
"Researchers use LRNOC's high-quality, real-time traffic data to create security tools," says Jeffrey O'Connell of Lincoln Laboratory's Cyber System Assessments Group. "With real data, we're forced to push the limit of our tools, making them more capable, resilient, and adaptable. It is a very effective way to prepare for the next cyber attack."
Armed with standard and Laboratory-developed tools, analysts sift through troves of network data looking for suspicious anomalies that may warrant further investigation. LRNOC serves as an incubator and a proving ground for next-generation tools that government sponsors look to adopt to protect their own networks from cyber attacks.
To ensure that the live data are protected, the LRNOC is on a network that is separate from the main Laboratory network. Laboratory researchers are bound by a user agreement that is consistent with ethical practices and Laboratory security policies and that regulates data removal and research activities.

Lincoln Laboratory researchers work in the Lincoln Research Network Operations Center (LRNOC) to identify and mitigate cyber threats. |
Because a vast amount of data, including system and application logs, network security appliance alerts, and raw traffic, are fed into LRNOC each day, researchers have created several tools to process the data. For example, one tool stores and aggregates each network packet entering and leaving the Laboratory network. The LRNOC infrastructure allows this tool to select packets on the basis of various features so analysts can define custom filters that capture and track communication with specific characteristics, such as heartbeat packets. Another tool, Scalable Cyber Analytic Processing Environment (SCAPE), works in a similar manner but creates feeds based on network information, such as logs and event data, rather than on raw network packets. SCAPE is a processing environment that monitors and correlates data feeds in real time to provide situational awareness about the state of the network.
These aggregator tools come in handy during attacks. Because LRNOC stores all network traffic data, researchers were able to carve out aggregated data from a period of time when the Heartbleed bug was active, gather pertinent data from that time period, and then investigate the selected data to determine abnormalities, such as a heartbeat packet. Researchers were then able to investigate the packets and work with SSD and ISD to determine if any sensitive information had been compromised.
Within LRNOC, research teams mainly work on two areas: monitoring Laboratory operations and developing or testing next-generation tools. Researchers collaborate with SSD and ISD to understand the challenges the network is up against, according to O'Connell. For example, if an LRNOC researcher finds suspicious traffic, he or she reports it to SSD and ISD staff, who potentially implement blocks on the network. If ISD finds a system on the network that might be compromised, they pass responsibility to SSD, who makes the final call on whether or not the system should be pulled from the network. If the system is pulled, SSD investigates it to find malicious components and may also isolate a malware sample and hand it back to the LRNOC for analysis. Working as a team, SSD, ISD, and LRNOC defend the Laboratory's network and support security protocols for sponsors.
"Our multifaceted, coordinated efforts in responding to not only daily incidents at the Laboratory but also several high-profile and potentially highly harmful exploits highlight the excellent collaboration among the various response teams, including LRNOC, ISD, and SSD," says Scott Mancini of SSD. "Their attention to detail and obvious dedication to protecting the Laboratory against daily threats are exceptional."
In addition to using LRNOC for defending the Laboratory's systems, research teams also use the network to develop security tools for government sponsors. Sponsors are eager to use programs created within LRNOC that can accurately protect their own networks from cyber attacks. For example, Laboratory researchers worked to enhance defender awareness of the specific types of scanning that adversaries conduct against the networks that they target. A Department of Defense sponsor requested and received a tool for fingerprinting five types of reconnaissance scans: Nmap, Strobe, Amap, Braa, Angry IP. This deliverable was developed and tested in the LRNOC by applying a detection algorithm on the real network data feeds in the LRNOC enclave.
Because LRNOC constantly evolves network security with each threat, its data are useful for developing current, accurate cyber defenses. "In just 30 minutes, LRNOC can see multiple reconnaissance activities probing the Laboratory's defenses," says O'Connell. "We keep seeing new threats and new ways to come out and be ahead of the curve." |